Anti-theft Computer Hardware & Software
The Anti-Theft Computer Hardware and Software system is a patented, dual layer hardware and software platform that delivers an escalating response to unauthorized computer access. The system integrates physical deterrence, automatic device lockdown, and real-time law enforcement notification, creating a breakthrough security solution for high-risk environments where traditional software-only defenses fall short.

One of the most damaging components of cybercrime is business downtime, which is responsible for an estimated $500 billion to $1 trillion in global losses each year. Because the United States accounts for a disproportionately high share of global cybercrime losses, U.S. companies bear a significant portion of this downtime burden. Additional business specific expenses include forensic investigations, legal and regulatory penalties, system restoration, and reputational harm, all of which contribute to the nation’s $320 billion annual impact.
Consumers are also heavily affected. In 2023 alone, 53.35 million U.S. citizens experienced some form of cybercrime, including identity theft, financial fraud, data breaches, and account takeovers. These incidents impose direct monetary losses as well as indirect costs such as time spent resolving fraud, credit damage, and device replacement.
The Anti-Theft Computer Hardware and Software directly targets the most expensive and disruptive category of cybercrime: unauthorized access leading to business interruption. By preventing intrusion at the physical point of contact—before data is accessed, systems are compromised, or operations are halted—the system addresses a loss category valued at $500 billion to $1 trillion annually and provides a level of protection unmatched by existing solutions.
Cybercrime has become one of the most expensive and rapidly growing threats to U.S. businesses and consumers. Recent analyses estimate that cybercrime now costs the United States approximately $320 billion annually as of 2023, with losses projected to surge to $1.82 trillion by 2028 if current trends continue. These costs arise from data breaches, ransomware attacks, identity theft, business interruption, intellectual property theft, and extensive recovery and remediation efforts.
Special Features
Two stage Unauthorized Access response system
Mild electric shock deterrent delivered through keyboard/interface
On-screen warning interrupt after first failed attempt
Full-system device lockdown after second failed attempt
Automated alarm activation
Automatic law enforcement notification
Integrated hardware + software security architecture
Tamper-resistant embedded shock delivery mechanism
Real-time intrusion detection
Data protection through forced shutdown protocols
Configurable security thresholds for enterprise use
Scalable for consumer, commercial, and government devices
PRODUCT FEATURES & BENEFITS
PRODUCT DETAILS
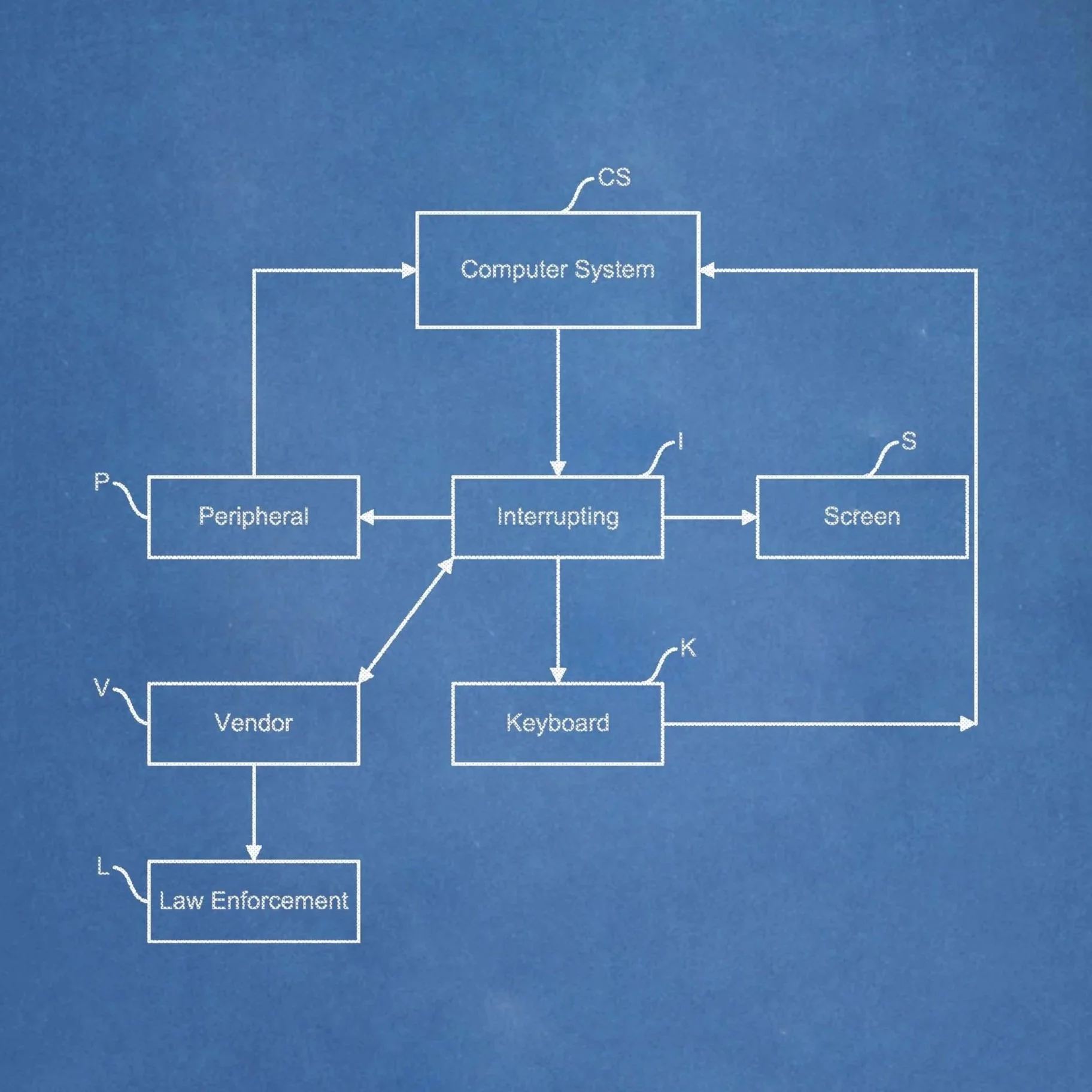
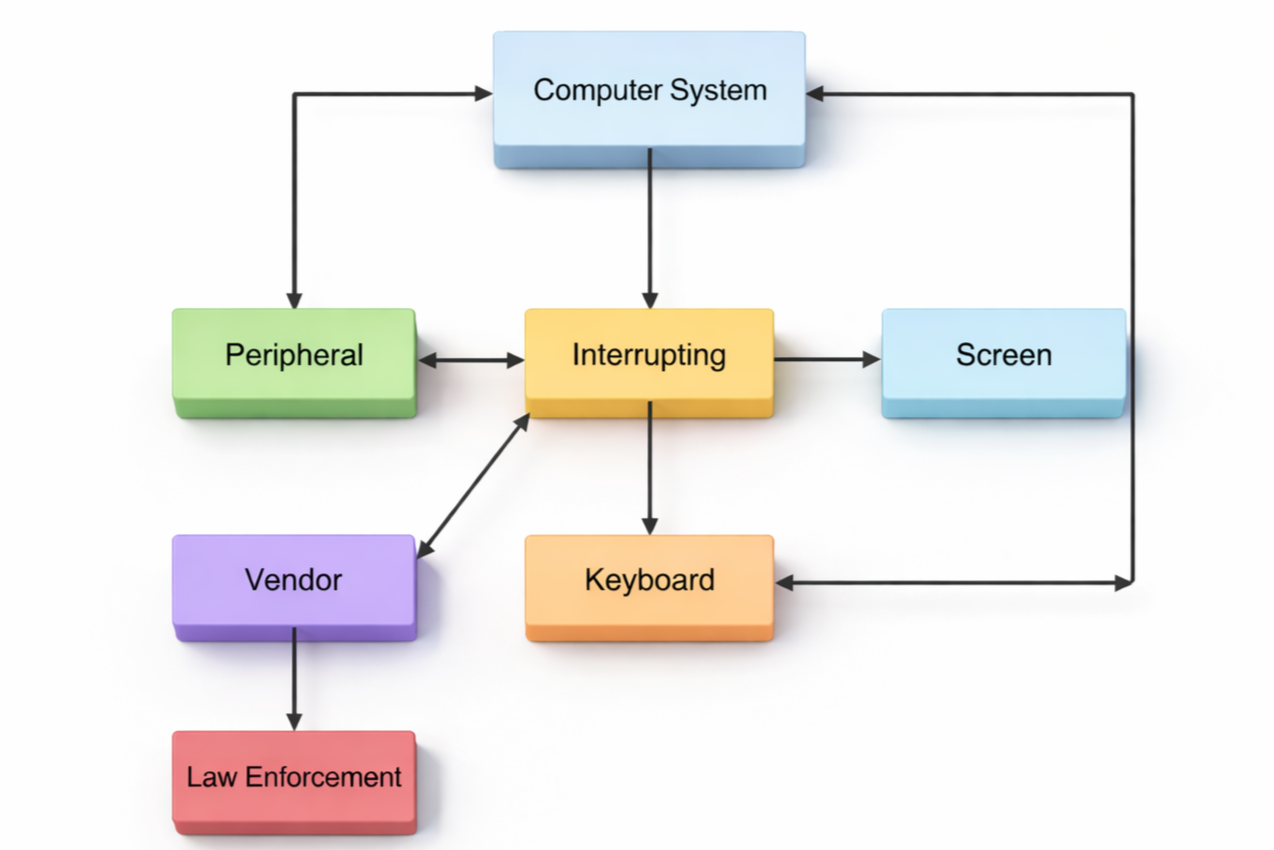
The Anti‑Theft Computer Hardware and Software system is an integrated, dual‑layer security platform engineered to prevent unauthorized access to computers and digital devices. Unlike traditional software‑only solutions, this patented system fuses physical deterrence, real‑time intrusion detection, and automated escalation protocols into a single, tamper‑resistant security architecture. Its purpose is simple yet powerful: stop unauthorized access at the point of contact—before a breach occurs.
At its core, the system continuously monitors login attempts and user interaction patterns. When an unauthorized access attempt is detected, the system initiates a two‑stage escalating response sequence designed to deter, interrupt, and ultimately prevent intrusion.

Stage 1 – First Unauthorized Attempt
Upon the first failed or unauthorized login attempt, the system activates a controlled, non‑lethal deterrent sequence:
Interrupt Triggered: The system immediately halts the login process and suspends further input.
On‑Screen Warning: A clear, high‑visibility warning message appears, notifying the user that an unauthorized attempt has been detected and logged.
Mild Electric Shock: A brief, low‑voltage electric shock is delivered through the keyboard or user interface. This shock is intentionally calibrated to be safe but unmistakably corrective, serving as a physical deterrent to discourage continued intrusion attempts.
This first stage is designed to stop opportunistic or low‑effort intruders before they escalate their attempts.
Stage 2 – Second Unauthorized Attempt
If a second unauthorized attempt occurs—indicating deliberate intrusion—the system escalates to a full security lockdown:
Second Interrupt Triggered: The system immediately terminates all active processes and blocks further interaction.
Device Lockdown: All input/output devices are disabled, preventing access to data, applications, or system resources.
Alarm Activation: An audible or silent alarm is triggered, depending on configuration, alerting nearby personnel or security staff.
Automatic Law‑Enforcement Notification: The system transmits a pre‑configured alert to law‑enforcement authorities or designated security contacts. This notification can include device location, timestamps, and intrusion metadata. This second stage ensures that persistent or malicious intruders are met with immediate, automated consequences.
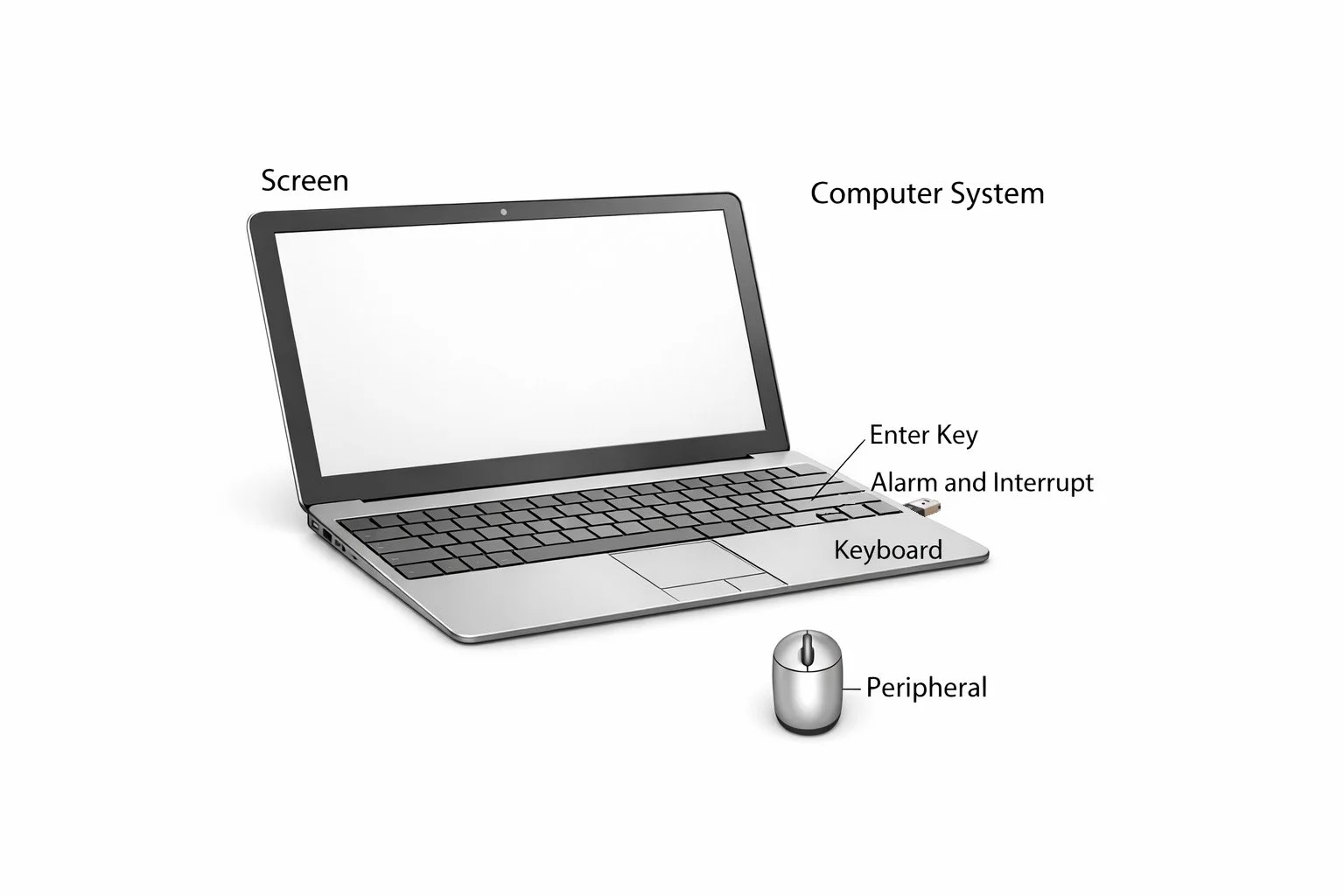
Hardware Component
The hardware subsystem includes a shock‑delivery module embedded directly into the keyboard, touchpad, or other user interface surface. This module is:
Tamper‑resistant, preventing removal or bypassing
Calibrated for safety, delivering a mild but effective deterrent
Integrated with system sensors, enabling real‑time detection of unauthorized interaction
Powered and regulated to ensure consistent performance without risk to the device
This hardware layer is what differentiates the system from all software‑only security solutions on the market.
Software Component
The software subsystem manages the intelligence and automation behind the platform. It includes:
Intrusion Detection Algorithms: Monitors login attempts, input patterns, and unauthorized access triggers.
Interrupt Management: Controls the timing and execution of Stage 1 and Stage 2 responses.
Escalation Logic: Determines when to deliver warnings, shocks, lockdowns, and notifications.
Communication Module: Sends automated alerts to law enforcement, security teams, or designated contacts.
System Logging: Records all intrusion attempts, timestamps, and system responses for audit and forensic review.
Together, the hardware and software components form a closed‑loop security system that responds instantly and autonomously to unauthorized access attempts
Materials needed to produce the Anti-Theft Computer Hardware and Software:
Embedded shock delivery module
Microcontroller for shock regulation
Secure firmware for interrupt logic
Device integrated sensors for unauthorized access detection
Software suite for system monitoring
Communication module for law enforcement alerts
Tamper resistant casing
Power regulation components
Keyboard/interface integration hardware
Optional enterprise grade configuration tools
The Anti‑Theft Computer Hardware and Software can elevate your product portfolio to new heights. We are seeking a long-term arrangement with a company to manufacture, market, and/or distribute this new technology based on the acquisition of the intellectual property rights . Contact us below
Contact Us
Our VP of Business Development, Amy Schleicher, is ready to answer any questions you may have.
Phone: 913-201-8025
E-mail: Amy@bankonip.com
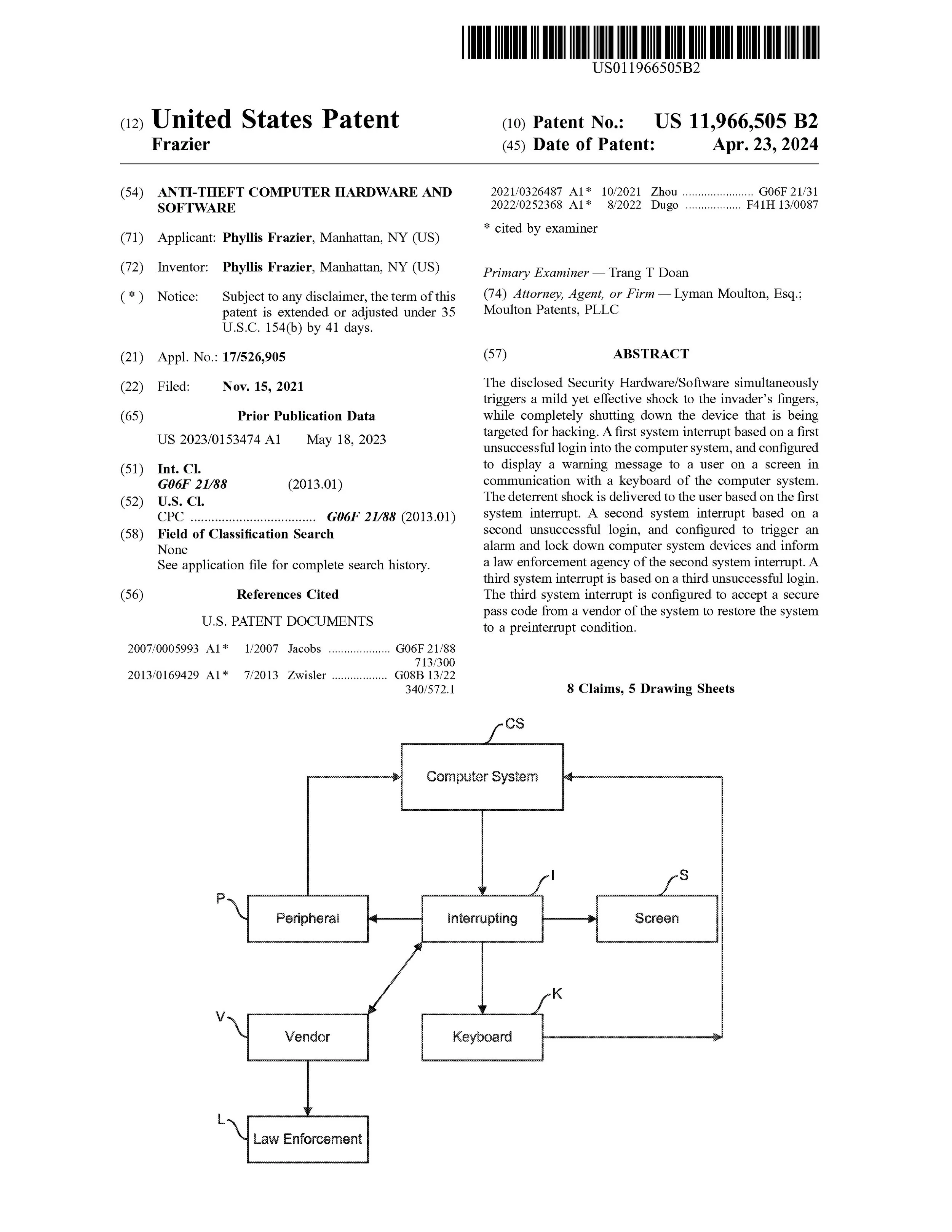
Patent Information
Inventor Highlight
Ms. Phyllis Frazier holds United States Utility Patent No. 11,966,505 filed on November 15, 2021, and issued on April 23, 2024. This patent for the Anti-Theft Computer Hardware and Software expires in 2041, commensurate with the filing date. This patent has 8 claims that protect the exclusive function of the Anti-Theft Computer Hardware and Software.
Social Media
Follow us in real time! Stay connected.
“There’s a way to do it better—find it”